Protecting users from government-backed hacking and disinformation
Google's Threat Analysis Group (TAG) works to counter targeted and government-backed hacking against Google and our users. This is an area we have invested in deeply for over a decade. Our daily work involves detecting and defeating threats, and warning targeted users and customers about the world’s most sophisticated adversaries, spanning the full range of Google products including Gmail, Drive and YouTube.
In the past, we’ve posted on issues like phishing campaigns, vulnerabilities and disinformation. Going forward, we’ll share more technical details and data about the threats we detect and how we counter them to advance the broader digital security discussion.
TAG tracks more than 270 targeted or government-backed groups from more than 50 countries. These groups have many goals including intelligence collection, stealing intellectual property, targeting dissidents and activists, destructive cyber attacks, or spreading coordinated disinformation. We use the intelligence we gather to protect Google infrastructure as well as users targeted with malware or phishing.
Phishing
We’ve had a long-standing policy to send users warnings if we detect that they are the subject of state-sponsored phishing attempts, and have posted periodically about these before. From July to September 2019, we sent more than 12,000 warnings to users in 149 countries that they were targeted by government-backed attackers. This is consistent (+/-10%) with the number of warnings sent in the same period of 2018 and 2017.
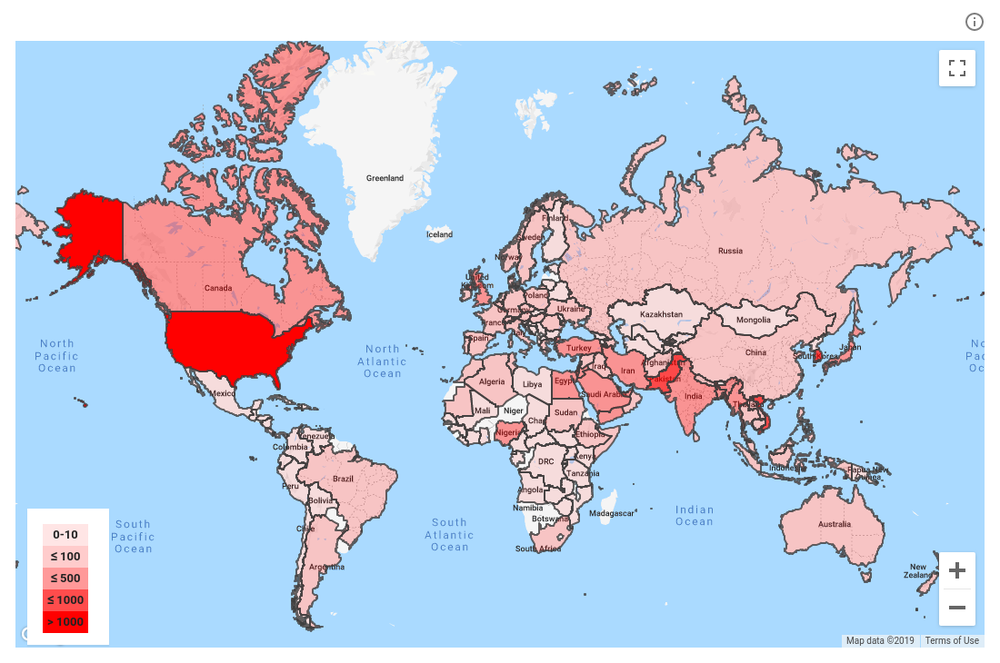
Distribution of government-backed phishing targets in Q3 (Jul-Sep 2019)
Over 90 percent of these users were targeted via “credential phishing emails” similar to the example below. These are usually attempts to obtain the target’s password or other account credentials to hijack their account. We encourage high-risk users—like journalists, human rights activists, and political campaigns—to enroll in our Advanced Protection Program (APP), which utilizes hardware security keys and provides the strongest protections available against phishing and account hijackings. APP is designed specifically for the highest-risk accounts and now has more than 15,500 users.
In the simple phishing example below, an attacker has sent a phishing email with a security alert lure from “Goolge” suggesting the user secure their account. The user clicks the link, enters their password, and may also get asked for a security code if they have two-factor authentication enabled, allowing the attacker to access their account.
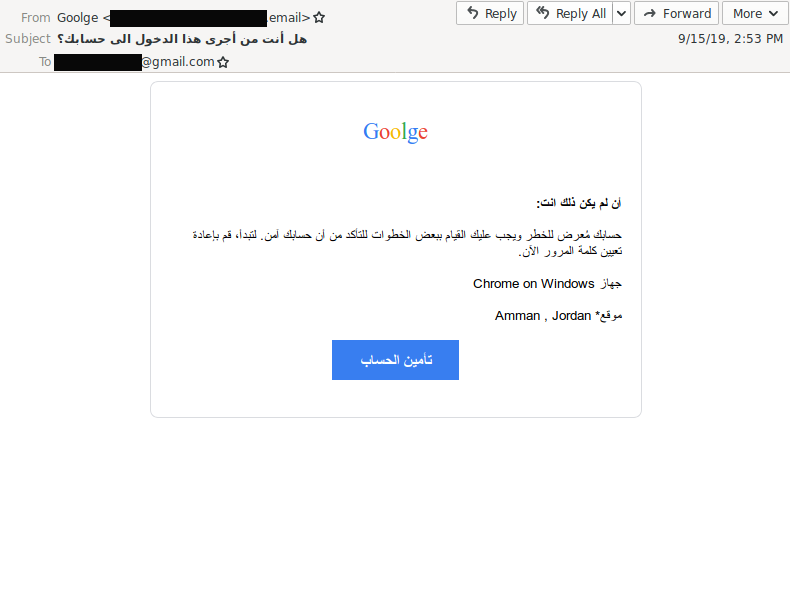
Sample lure used to phish Gmail users
Threat detection
Last week at CyberwarCon, we presented analysis about previously undisclosed campaigns from a Russia-nexus threat group called “Sandworm” (also known as “Iridium”). It’s a useful example of the type of detailed threat detection work that TAG does. Although much of Sandworm’s activity targeting Ukraine and their attacks against the 2018 Winter Olympics have been covered publicly, some campaigns have not been reported.
In December 2017, TAG discovered a series of campaigns from Sandworm attempting to deploy Android malware. The first campaign targeted users in South Korea, where Sandworm was modifying legitimate Android applications with malware. They then uploaded these modified apps to the Play Store using their own attacker-controlled developer accounts. During this campaign, Sandworm uploaded eight different apps to the Play Store, each with fewer than 10 total installs.
Malicious apps targeting users in South Korea
We also identified an earlier September 2017 Android campaign from Sandworm where they used similar tactics and deployed a fake version of the UKR.net email app on the Play Store. This application had approximately 1,000 total installs. We worked with our colleagues on the Google Play Protect Team to write detections for this malware family, and eliminate it.
In November 2018, we saw evidence that Sandworm shifted from using attacker-controlled accounts to try and upload malicious apps to compromising legitimate developers. Throughout November, Sandworm targeted software and mobile app developers in Ukraine via spear phishing emails with malicious attachments. In at least one case, they compromised an app developer with several published Play Store apps—one with more than 200,000 installs.
After compromising the developer, Sandworm built a backdoor in one of the legitimate apps and attempted to publish it on the Play Store. They did this by adding their implant code into the application package, signing the package with the compromised developer’s key, and then uploading it to the Play Store. However, the Google Play Protect team caught the attempt at the time of upload. As a result, no users were infected and we were able to re-secure the developer’s account.
Disinformation
TAG is one part of Google and YouTube’s broader efforts to tackle coordinated influence operations that attempt to game our services. We share relevant threat information on these campaigns with law enforcement and other tech companies. Here are some examples that have been reported recently that TAG worked on:
-
TAG recently took action against Russia-affiliated influence operations targeting several nations in Africa. The operations use inauthentic news outlets to disseminate messages promoting Russian interests in Africa. We have observed the use of local accounts and people to contribute to the operation, a tactic likely intended to make the content appear more genuine. Targeted countries included the Central African Republic, Sudan, Madagascar, and South Africa, and languages used included English, French, and Arabic. Activity on Google services was limited, but we enforced across our products swiftly. We terminated the associated Google accounts and 15 YouTube channels, and we continue to monitor this space. This discovery was consistent with recent observations and actions announced by Facebook.
-
Consistent with a recent Bellingcat report, TAG identified a campaign targeting the Indonesian provinces Papua and West Papua with messaging in opposition to the Free Papua Movement. Google terminated one advertising account and 28 YouTube channels.
Partnerships
TAG works closely with other technology companies—including platforms and specialized security firms—to share intelligence and best practices. We also share threat information with law enforcement. And of course there are multiple teams at Google at work on these issues with whom we coordinate.
Going forward, our goal is to give more updates on the attacks that TAG detects and stops. Our hope is that shining more light on these actors will be helpful to the security community, deter future attacks, and lead to better awareness and protections among high-risk targets.
by Shane HuntleyThreat Analysis Group via The Keyword
Comments
Post a Comment